Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
[ad_1]
Researchers from the University of California have discovered a new class of malware capable of draining cryptocurrency wallets and injecting malicious code into software environments, and such crypto theft has already occurred in real life.
A formal study published on arXiv on April 8, 2026, titled “Measuring Man-in-the-Middle Risk in a Large Communication Chain,” showed that 428 routers tested AI APIs. The study found that 9 of them injected malicious code, 17 of which obtained AWS researchers’ credentials, while one free router extracted ETH from a private key monitored by researchers.
The attack site is part of AI agent routing, a foundation that has grown rapidly with… Integrating AI agents into blockchain implementation. The question was no longer whether the threat is a hypothetical one, but how many compromised routers are serving users’ needs.
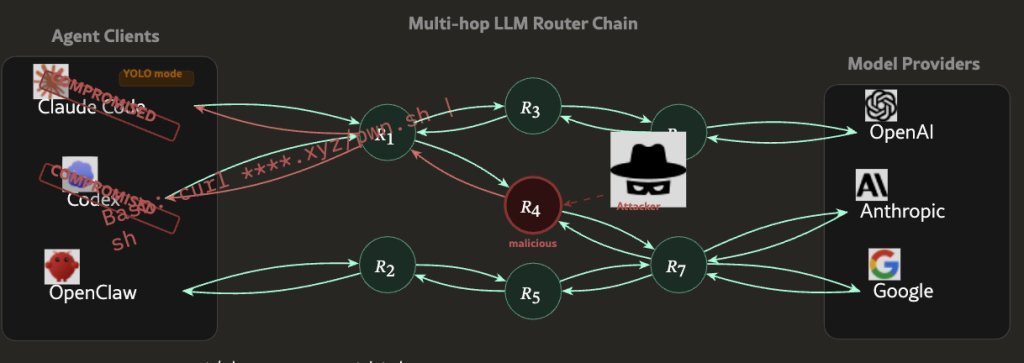
The main language model (LLM) APIs are designed to provide simple requests and responses: the client sends a request, the router passes it to the instance provider, and the response is returned.
Malicious routers take advantage of this reliable method; They act as layer proxies between those exchanges, reading and writing complete JSON payloads going both ways.
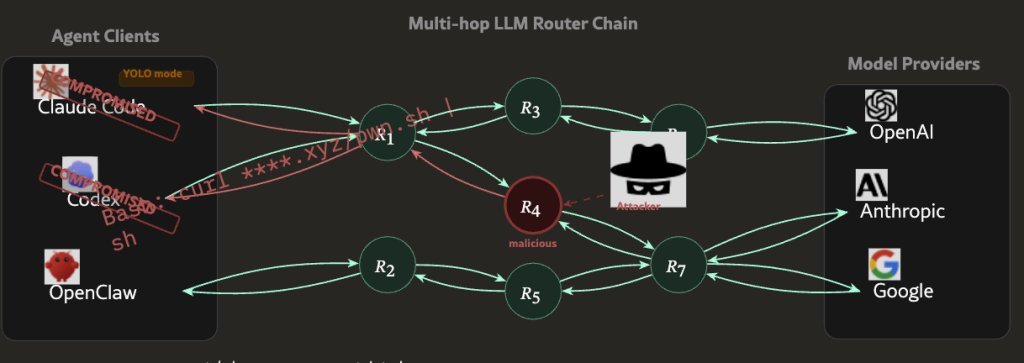
There are no cryptographic standards that control what a router can check or change during transmission. A malicious router sees the raw request, the form response, and everything in it – including private keys, API credentials, wallet return statements, or code that is created for the sending environment.
The device can change the response before it reaches the user, enter other codes to release the code, or silently transmit the confirmation to the external endpoint.
UCLA researchers created an agent they named “My” to test four types of attacks against human behavior, specifically following YOLO representation steps where the agent takes action without human confirmation at each step.
Two of the 428 routers tested adaptive encryption methods; One of them waited 50 API calls before triggering malicious behavior so it wouldn’t be detected on the first try. This is not a random data hacking tool, it is a tool designed to bypass surveys.
A poisonous attack vector increases the risk significantly. When OpenAI API keys are disposed of through a compromised system, the damage can escalate quickly; 2.1 billion codes were processed, and 99 clues were revealed in 440 sections of the Codex in a laboratory led by researchers alone.
The problem is not that there are third-party APIs, but that the whole type of trust in AI agents assumes that the method is neutral, and at the moment there is no incentive method that looks at this idea at scale.
Developers who create blockchains, decentralized finance (DeFi), and independent agents often run API calls through third-party tools.
Free routers that come from the public domain – the category where 8 out of 9 malicious code injectors are found – are widely used because they reduce the cost of infrastructure that supports a large variety of languages. And it is The automation system in DeFi relies on external information and the connection of providersThe layering process becomes a very attractive target.
Modern wallet security – such as hardware wallets, multi-signature settings, and offline key storage – does not protect against a router that tampers with the private key before it reaches the signature, or injects malicious code into a transmission script that is later executed over the Internet.
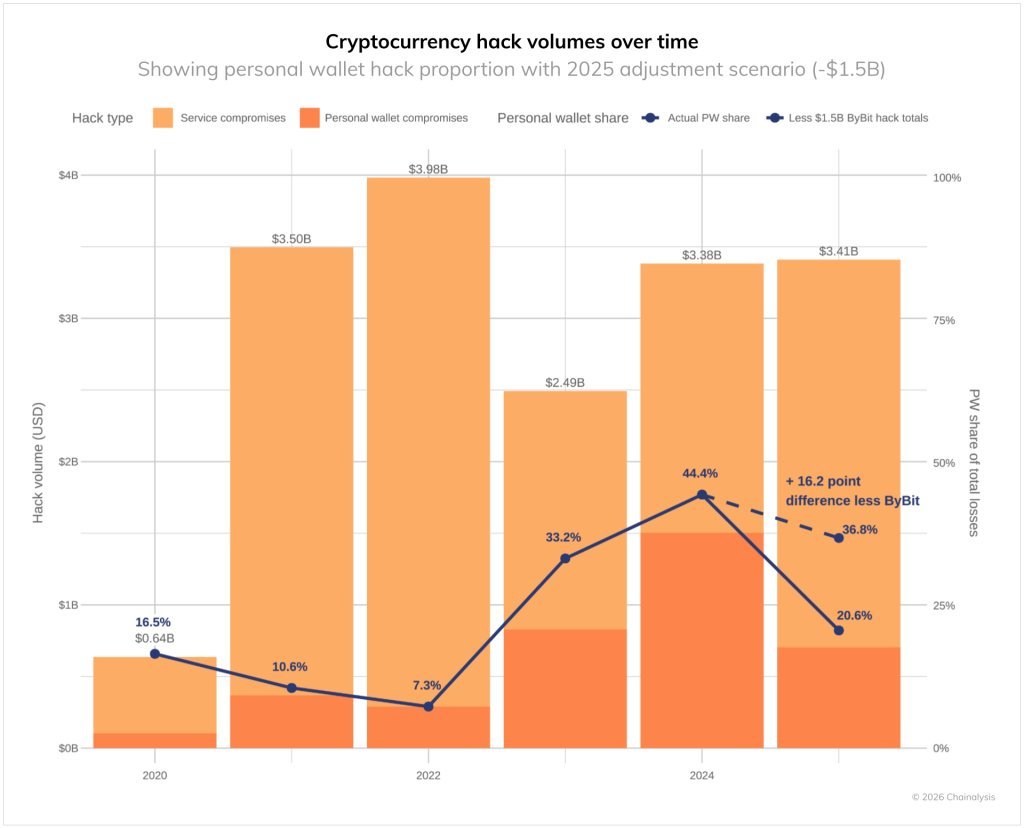
The annual loss of crypto theft has already reached $1.4 billion. This attack vector does not need to break encryption, but to compromise a central device that most users do not see.
YOLO’s independent sectors are the most vulnerable. When a user performs multiple steps without a human check to verify, the malicious router has a large window to operate, and the user has no way of knowing what they are doing.
The founder of Solayer, known as @Fried_rice, highlighted his findings through the Platform
LLM’s 26 routers are intercepting phone calls and stealing documents. One killed our client’s $500k wallet.
We also managed to kill routers to send traffic to us. In a few hours, we can get more than ~400 hosts directly.
See our paper: https://t.co/zyWz25CDpl pic.twitter.com/PlhmOYz2ec
– Chaofan Shou (@Fried_rice) April 10, 2026
The defenses recommended by the researchers come from the client side: error gating that stops execution when unknown responses are detected, filtering abnormal responses, and logging logs that cannot be processed by the router itself. In the long run, the UCLA team calls for standards for digital signatures that make responses from large-scale languages more reliable, a building block that makes … Oracle’s network integrity is critical to the design And it’s not just speculation.
A note Warning: AI infrastructure attacks are draining cryptocurrency wallets appeared for the first time Cryptonews Arabic.
[ad_2]
Source link