Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
[ad_1]
Kraken confirmed on Monday that it had been tested by a criminal group with internal videos containing customer data, and the cryptocurrency trading platform made clear its refusal to comply with their demands.
Nick Percoco, the company’s head of security, revealed the threat through X on April 13, 2026, explaining that the company is working with the authorities in several places to track down and arrest the perpetrators.
This rejection is the right choice and a reading indicator at a time when trust in trading platforms is fragile.
Important points:
This operation was not performed due to protocol accident or theft. The legacy of both the February 2025 event and the recent threat was through internal recruitment; Where people were insulted within the organization Kraken By providing access to internal systems, allowing for review work rather than complete hacking.
Access appears to have been limited to read-only, which was enough to capture customer data on video without triggering the active interface.
Percoco confirmed that Kraken received information about the video showing customer information from its internal crypto system, the same method used in the February 2025 case, where a similar video appeared in court.
Kraken Security Update
We are currently under attack from a group of criminals who are threatening to release videos of our internal operations and customer data being displayed if we do not comply with their demands. It is important to start with the most important facts: our machine was not…
— Nick Percoco (@c7five) April 13, 2026
In both cases, an insider was identified as being involved. The hackers are threatening to distribute the videos and customer communications to local radio and television stations unless Kraken complies. The exact amount of money required for the fraud has not been disclosed publicly.
Percoco described this strategy as deliberate and dangerous, saying: “We have been cooperating with industry partners and law enforcement officials to investigate and disrupt recruitment activities targeting not only crypto companies, but also gaming and communications organizations.”
This isn’t just a waste of opportunity, it’s a way to connect people to a service that works at a price point, and Kraken making this clear is an important way for all companies to respond.
Reports indicate that Crypto theft vectors are increasingly focusing on access and infrastructure rather than exploiting network software vulnerabilities.Recruiting falls within these risks.
Kraken has not publicly identified the categories of data captured in the videos, whether “know your customer” (KYC), wallet addresses, transaction history, or account metadata.
But what has been confirmed is that around 2,000 people have been exposed, and Kraken said it has already contacted everyone at risk. Access was read only, and internal systems were not compromised in the details of the massive data leak.
The risk of affected users is not account takeover, where there is no money to be found, but it is focused on technical and physical features.
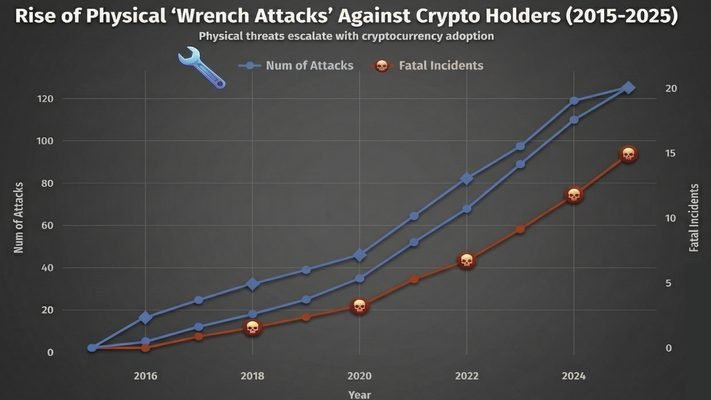
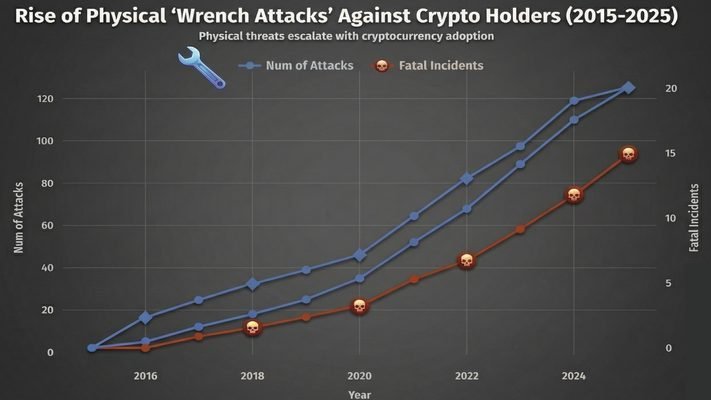
With names, addresses, and account data in the hands of hackers, the affected users became the target of the company’s targeted attacks. TRM imageswhich resulted in a loss of more than $40 million last year.
This number may be lower, due to the underreporting of such incidents. Kraken’s move to meet affected users is the right thing to do; However, it has not yet been determined whether this communication included specific security instructions, suggestions for using physical security keys, changing addresses, or increased vigilance.
A note The Kraken website rejects submissions to scams and hackers who threaten to release customer data appeared for the first time Cryptonews Arabic.
[ad_2]
Source link