Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124

Russian cybercriminals are likely responsible for laundering more than $35 million in cryptocurrency stolen from LastPass users, according to a report from blockchain intelligence firm TRM Labs.
The analysis linked the drain of cryptocurrency wallets over a period of several years to the hacking of the LastPass password manager in 2022. It indicated that the stolen funds moved through an illicit financial infrastructure linked to secret Russian cybercrime.
Sponsored
Sponsored
TRM Labs researchers found that the attackers used privacy protocols to hide the money trail, but they were in the end. They directed the money to Russian platforms.
According to the report, the perpetrators continued to steal assets from the compromised vaults until the end of 2025.
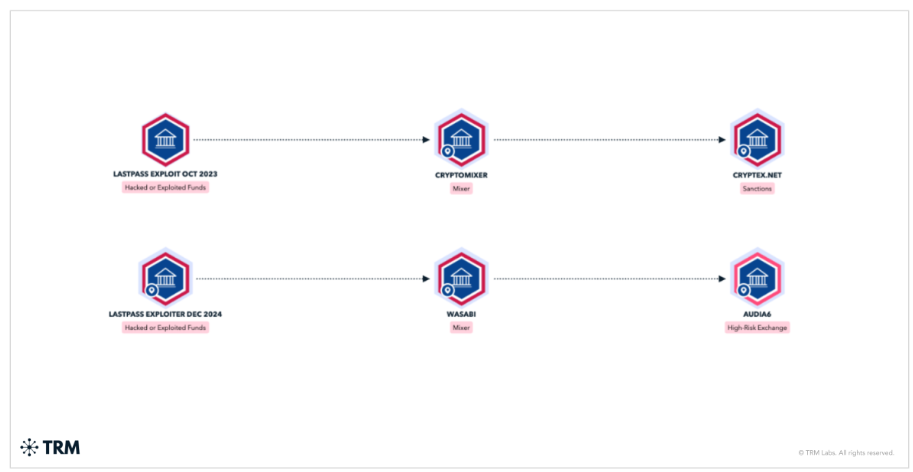
Malicious actors have systematically laundered stolen funds through exits historically used by Russian threats. One of these platforms was Cryptex, an exchange that is currently subject to censorship US Office of Foreign Assets Control (OFAC).
TRM Labs said it had identified a “consistent signature on the chain” linking the thefts to a coordinated group.
Attackers have repeatedly converted non-Bitcoin assets into Bitcoin using spot exchange services. Then the money was transferred Exchange services like Wasabi Wallet and CoinJoin.
Sponsored
Sponsored
These tools are designed to pool funds from multiple users to scramble transaction records, making them theoretically untraceable.
However, the report highlights a major failure of these privacy technologies. Analysts were able to “deconstruct” transactions using behavioral continuity analysis.
Investigators tracked down specific fingerprints, such as how the wallet software imported private keys, and managed the mix. This allowed them to track the digital currency through privacy protocols and track its final deposit on Russian exchanges.
In addition to Cryptex, investigators traced approximately $7 million in stolen funds to Odi6, another exchange service operating in the Russian cybercriminal ecosystem.
The report notes that the portfolios that reacted to the mix show ” Operational ties” with Russia Before and after the washing process. This suggests that the pirates did not just rent infrastructure, but operated directly from the region.
The findings highlight the role of Russian cryptocurrency platforms in enabling global cybercrime.
By providing liquidity and ramps for stolen digital assets, these exchanges allow criminal groups to monetize data breaches with Avoiding the application of international law.