Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124
Physical Address
304 North Cardinal St.
Dorchester Center, MA 02124

A cryptocurrency trader lost $50 million worth of Tether USDT after suffering a sophisticated attack known as an “address poisoning” attack.
A December 20 report from blockchain security firm Scam Sniffer said the attack began after the victim sent a low-value test transaction of $50 to his own address.
Sponsored
Sponsored
Merchants take this standard precaution to ensure that funds are sent to the correct address.
However, this activity alerted an automated script from the attacker, which responded immediately Create a similar “fake” wallet address.
The fake address is designed to match the address of the intended recipient at the beginning and end of the chain of letters and numbers, with visible differences only in the middle letters, making the fraud difficult to detect at first glance.
The attacker sent a small amount of cryptocurrency from the fake address to the victim’s wallet.
Sponsored
Sponsored
Performing that transaction resulted in the fraudulent address being included in the victim’s recent transaction history, as many wallet interfaces only display part of the address details.
The victim relies on this visual shortcut, copying the address from his transaction history without checking the full chain. Instead of transferring the funds to a secure personal wallet, the trader transferred 49,999,950 USDT directly to the attacker.
According to blockchain records, you go The malicious attacker immediately upon receipt of funds to reduce the risk of confiscation of assets. The attacker directly transferred the stolen USDT – which could have been frozen by its issuer –To DAI stablecoin using MetaMask Swap.
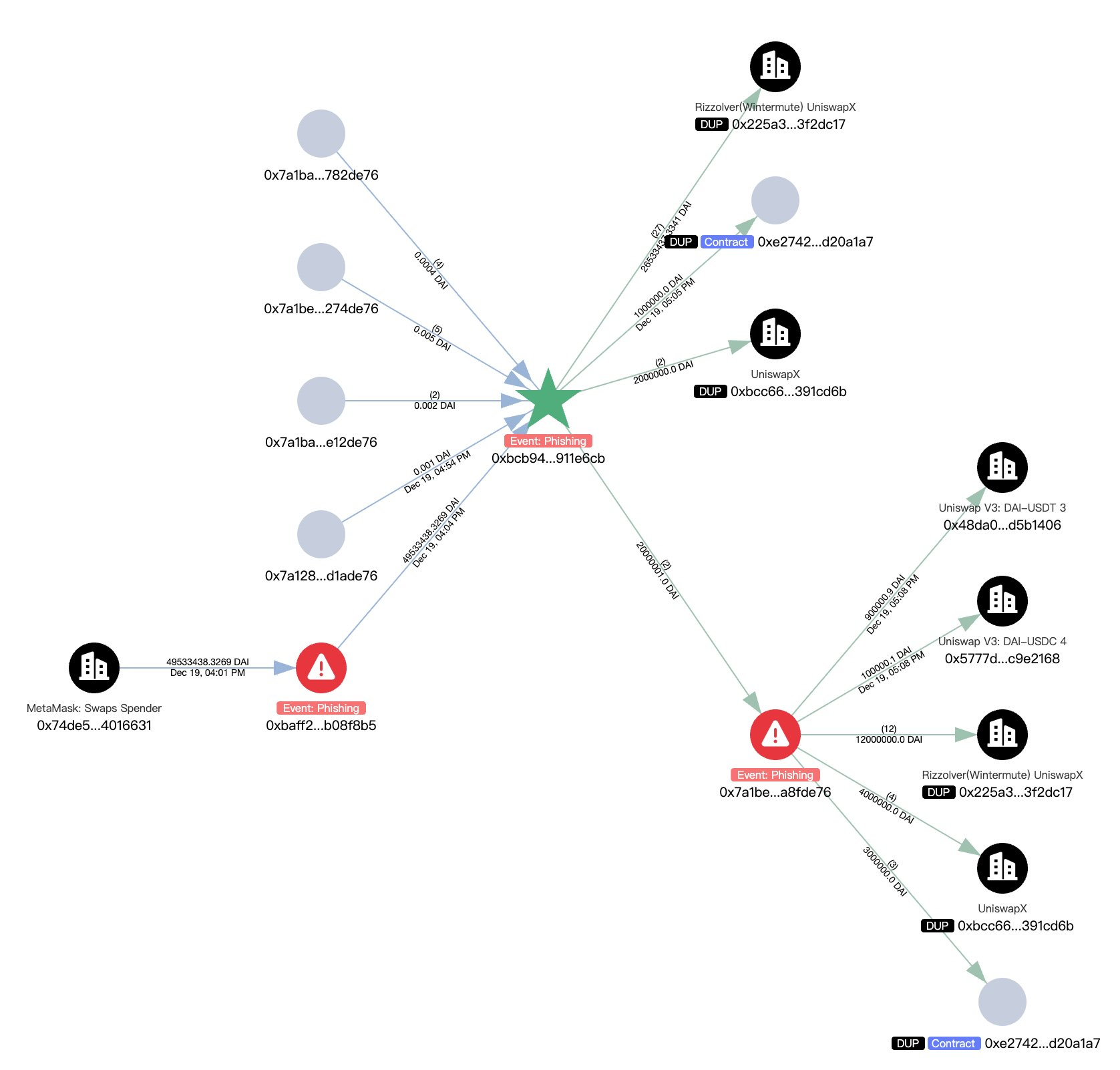
The attacker converted the funds into approximately 16,680 ETH.
Sponsored
Sponsored
To further hide the trace of the transactions, the attacker deposited ETH in Tornado Cash. This decentralized application provides a mixing service designed to separate the visual link between sender and recipient addresses.
Attempting to recover the asset, the victim sent a message on the chain offering a white hat reward of $1 million in exchange for recovering 98% of the stolen funds.
“We have formally filed a criminal case. With the help of law enforcement agencies, cyber security agencies, and numerous blockchain protocols, we have already gathered significant intelligence and action on your activities,” the letter said. He said.
Sponsored
Sponsored
The letter warned that the victim would take “relentless” legal action if the attacker did not comply within 48 hours.
The victim stated: “If you do not comply: We will escalate the matter through legal and international law enforcement channels. Your identity will be revealed and shared with the appropriate authorities. We will relentlessly pursue criminal and civil processes until full justice is served. This is not a solicitation. You are given one last chance to avoid irreversible consequences.”
The incident highlights an ongoing vulnerability in how cryptocurrency wallets display transaction information and how attackers exploit user behavior instead of vulnerabilities in the blockchain code.
Security analysts have repeatedly warned that wallet providers’ practice of shortening long address strings for usability and design purposes creates constant risk.
If this issue is not resolved, attackers will likely continue to exploit the tendency of users to check only the first and last characters of an address.